LAM manages various types of user accounts. This includes address book entries, Unix, Samba, Kopano and much more.
Account list settings:
The user list includes two special options to change how your users are displayed.

Translate GID number to group name: By default the user list can show the primary group IDs (GIDs) of your users. There are often cases where it is more suitable to show the group name instead. This can be done by activating this option. Please note that LAM will execute more LDAP queries which may result in decreased performance.

Show account status: If you activate this option then there will be an additional column displayed that shows if the account is locked or expired. You can see more details when moving the mouse cursor over the lock icon. This function supports Unix, Samba, PPolicy, Windows and 389ds locking+deactivation.

Password:
Click the "Set password" button to change the user's password(s). Depending on the active account modules LAM will offer to change multiple passwords at the same time.
If a module supports to enforce a password change then you will see the appropriate checkbox. LAM Pro also offers to send the password via email/SMS after the account is saved. Email options are specified in your LAM server profile and SMS options in main configuration.

Quick account (un)locking:
When you edit an user then LAM supports to quickly lock/unlock the whole account. This includes Unix, Samba and PPolicy. LAM can also remove group memberships if an account is locked.
You will see the current status of all account parts in the title area of the account.

If you click on the lock icon then a dialog will be opened to change these values. Depending on which parts are locked LAM will provide options to lock/unlock account parts.


This module is the most common basis for user accounts in LAM. You can use it stand-alone to manage address book entries or in combination with Unix, Samba or other modules.
The Personal module provides support for managing various personal data of your users including mail addresses and telephone numbers. You can also add photos of your users. If you do not need to manage all attributes then you can deactivate them in your server profile.
Configuration
Please activate the module "Personal (inetOrgPerson)" for users.

The module manages lots of fields. Probably, you will not need all of them. You can hide fields in module settings.
In advanced options you may also set fields to read-only (for existing accounts) and define limits for photo files. Additionally, you can add an "ou=addressbook" subentry to each user in case you manage user addressbooks.

User management

User certificates can be uploaded and downloaded. LAM will automatically convert PEM to DER format.

Table 4.1. LDAP attribute mappings
| Attribute name | Name inside LAM |
|---|---|
| businessCategory | Business category |
| carLicense | Car license |
| cn/commonName | Common name |
| departmentNumber | Department(s) |
| description | Description |
| employeeNumber | Employee number |
| employeeType | Employee type |
| facsimileTelephoneNumber/fax | Fax number |
| givenName/gn | First name |
| homePhone | Home telephone number |
| initials | Initials |
| jpegPhoto | Photo |
| l | Location |
| labeledURI | Web site |
| mail/rfc822Mailbox | Email address |
| manager | Manager |
| mobile/mobileTelephoneNumber | Mobile number |
| organizationName/o | Organisation |
| ou | Organizational unit |
| pager | Pager number |
| physicalDeliveryOfficeName | Office name |
| postalAddress | Postal address |
| postalCode | Postal code |
| postOfficeBox | Post office box |
| registeredAddress | Registered address |
| roomNumber | Room number |
| sn/surname | Last name |
| st | State |
| street/streetAddress | Street |
| telephoneNumber | Telephone number |
| title | Job title |
| userCertificate | User certificates |
| uid/userid | User name |
| userPassword | Password |
Wildcards
This module provides the following wildcards (others may be provided by other modules). Add a "_" after the "$" to get the value in lower-case (e.g. "$_firstname").
$firstname: First name
$lastname: Last name
$user: User name
$commonname: Common name
$email: Email address
You can use them in the following input fields on user edit screen:
Common name
Description
Mail
Postal address
Registered address
Web site
Use this when some of your data always follows the same schema. E.g. setting "$firstname $lastname" for the common name field can be used like this to get "First Last". You can set the wildcards in profile editor so they are automatically applied for new users.


The Unix module manages Unix user accounts including group memberships.
There are several configuration options for this module:
UID generator: LAM will suggest UID numbers for your accounts. Please note that it may happen that there are duplicate IDs assigned if users create accounts at the same time. Use an overlay like "Attribute Uniqueness" (example) if you have lots of LAM admins creating accounts.
Fixed range: LAM searches for free numbers within the given limits. LAM always tries to use a free UID that is greater than the existing UIDs to prevent collisions with deleted accounts.
Samba ID pool: This uses a special LDAP entry that includes attributes that store a counter for the last used UID/GID. Please note that this requires that you install the Samba schema and create an LDAP entry of object class "sambaUnixIdPool".
Magic number: Use this if your LDAP server assigns the UID numbers automatically (e.g. DNA by 389 server). Enter the server's magic number setting.
Password hash type: If possible use CRYPT-SHA512 or SSHA to protect your user's passwords. The option SASL will set the password to "{SASL}<user name>". If you want to use an LDAP EXOP password operation to update the password then select LDAP_EXOP.
Login shells: List of valid login shells that can be selected when editing an account.
Hidden options: Some input fields can be hidden to simplify the GUI if you do not need them.
Set primary group as memberUid: By default primary group membership is not set on group objects but only on user (gidNumber). Activate this if you need to have the primary group membership in group object, too.
Do not add object class: This is for Windows only. When the checkbox is activated then the posixAccount object class will not be added to a user.
User name suggestion: The user name is automatically filled as specified in the configuration (default smiller for Steve Miller). Of course, the suggested value can be changed any time. Common name is also filled with first/last name by default.


Group memberships can be changed when clicking on "Edit groups". Here you can select the Unix groups and group of names memberships.
To enable "Group of names" please either add the groups module "groupOfNames"/"groupOfUniqueNames" or add the account type "Group of names".

You can also create home directories for your users if you setup lamdaemon. This allows you to create the directories on the local or remote servers.
It is also possible to check the status of the user's home directories. If needed the directories can be created or removed at any time.

Wildcards
This module provides the following wildcards (others may be provided by other modules). Add a "_" after the "$" to get the value in lower-case (e.g. "$_user").
$user: User name
$group: Group name (not numeric number)
You can use them in the following input fields on user edit screen:
Common name
Gecos
Home directory
Use this when some of your data always follows the same schema. E.g. using "/home/$user" in home directory field can be used like this to get "/home/myuser". You can set the wildcards in profile editor so they are automatically applied for new users.


This module manages memberships in group of (unique) names and also group of members.
Please note that this module cannot be used if the Unix module is active. In this case group memberships may be managed with the Unix module.
Configuration
To activate this feature please add the user module "Group of names (groupOfNamesUser)" to your LAM server profile.

The module automatically detects if groups are based on "groupOfNames", "groupOfUniqueNames" or "groupOfMembers" and sets the correct attribute.

LAM can manage role memberships in organizationalRole objects. To activate this feature please add the user module "Roles (organizationalRoleUser)" to your LAM server profile.

User editing
Now, there will be a new tab "Roles" when you edit your user accounts. Here you can select the role memberships.

LAM supports the management of the LDAP substitution of /etc/shadow. Here you can setup password policies for your Unix accounts and also view the last password change of a user.

Configuration
Please add the module "NIS net groups (nisNetGroupUser)" to the list of active user modules.

User editing
You will now see a new tab when editing users. Here you can assign memberships in NIS net groups and also set host/domain.

LAM Pro allows your users to reset their passwords by answering a security question. The reset link is displayed on the self-service page. Additionally, you can set question + answer in the admin interface.
Please note that self-service and LAM admin interface are separated functionalities. You need to specify the list of possible security questions in both self-service profile(s) and server profile(s).
Schema installation
Please install the LDAP schema as described here.
Activate password self reset module
Please activate the password self reset module in your LAM Pro server profile.

Now select the tab "Module settings" and specify the list of possible security questions. Only these questions will be selectable when you later edit accounts unless you explicitly allow to enter custom questions. LAM Pro supports to set up to three security questions per user.
If you do not want to set backup email addresses then you can hide this option.

Edit users
After everything is setup please login to LAM Pro and edit your users. You will see a new tab called "Password self reset". Here you can activate/remove the password self reset function for each user. You can also change the security question and answer.
If you set a backup email address then confirmation emails will also be sent to this address. This is useful if the user password grants access to the user's primary mailbox. So passwords can be unlocked with an external email address.
Hint: You can add the passwordSelfReset object class to all your users with the multi edit tool.
Samba 4 note: Due to a bug in Samba 4 you need to add the extension, save, and then select a question and set the answer. If you add the extension, set question/answer and then save all together this will cause an LDAP error and no changes will be saved.

You can specify a list of valid host names where the user may login. If you add the value "*" then the user may login to any host. This can be further restricted by adding explicit deny entries which are prefixed with "!" (e.g. "!hr_server").
Please note that your PAM settings need to support host restrictions. This feature is enabled by setting pam_check_host_attr yes in your /etc/pam_ldap.conf. When it is enabled then the account facility of pam_ldap will perform the checks and return an error when no proper host attribute is present. Please note that users without host attribute cannot login to such a configured server.

LAM supports full Samba 3 user management including logon hours and terminal server options.
The module is enabled by adding "Samba 3 (sambaSamAccount)" to your user modules.

In the configuration options you can enable password history checking. Depending on your LDAP server you might need ascending or descending order. Just switch the setting if the password history is not correctly updated.
In case you have no very old Windows clients (e.g. Windows 98) it is recommended to disable LM hashes. They are considered to be insecure.
You can also hide some input fields if you do not need them.

After configuring the module you will see the Samba 3 tab when you edit a user.

Wildcards
You can use wildcards in the following input fields on user edit screen:
Display name
Home path
Profile path
Logon script
Use this when some of your data always follows the same schema. E.g. using "\\server\$user" in home path field can be used like this to get "\\server\myuser". You can set the wildcards in profile editor so they are automatically applied for new users.
Logon hours

You can also setup terminal server settings.

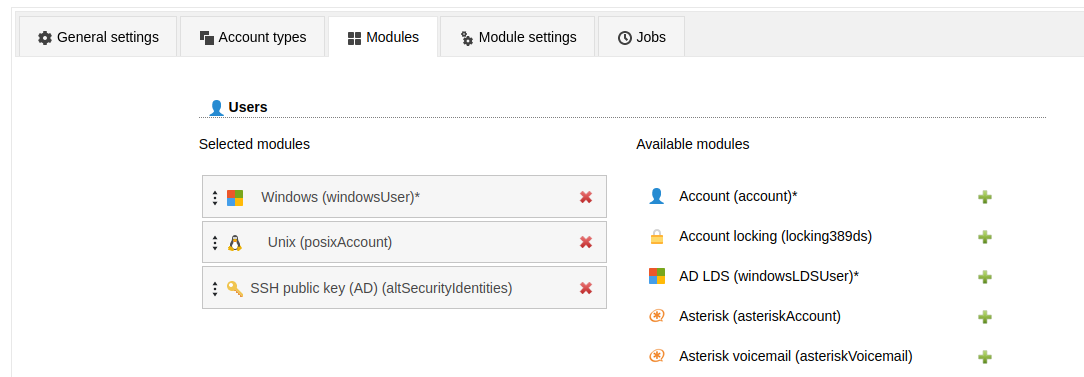
Please activate the account type "Users" in your LAM server profile and then add the user module "Windows (windowsUser)(*)".

The default list attributes are for Unix and not suitable for Windows (blank lines in account table). Please use "#cn;#givenName;#sn;#mail" or select your own attributes to display in the account list.
The following virtual attributes can be shown in the user list. These are no real LDAP attributes but extra data that can be shown by LAM.
memberof_count: number of entries in attribute "memberOf"

On tab "Module settings" you can specify the possible Windows domain names and if pre-Windows 2000 user names should be managed.
NIS support is deactivated by default. Enable it if needed.
You can also set maximum values for user photos in advanced options.

Now you can manage your Windows users and e.g. assign groups. You might want to set the default domain name in the profile editor.
Attention:
Password changes require a secure connection via ldaps://. Check your LAM server profile if password changes are refused by the server.
Your server must run a 64bit operating system. Otherwise, the module might not work.


Wildcards
This module provides the following wildcards (others may be provided by other modules). Add a "_" after the "$" to get the value in lower-case (e.g. "$_firstname").
$personaltitle: Personal title
$firstname: First name
$lastname: Last name
$user: User name
$commonname: Common name
$email: Email address
You can use them in the following input fields on user edit screen:
Common name
Display name
Email
Email alias
Home directory
Profile path
Script path
User name
User name (pre W2K)
Use this when some of your data always follows the same schema. E.g. setting "$firstname $lastname" for the common name field can be used like this to get "First Last". You can set the wildcards in profile editor so they are automatically applied for new users.


Please activate the account type "Users" in your LAM server profile and then add the user module "AD LDS (windowsLDSUser)(*)".

The default list attributes are for Unix and not suitable for AD LDS (blank lines in account table). Please use "#cn;#givenName;#sn;#mail" or select your own attributes to display in the account list.
The following virtual attributes can be shown in the user list. These are no real LDAP attributes but extra data that can be shown by LAM.
memberof_count: number of entries in attribute "memberOf"

On tab "Module settings" you can specify the possible Windows domain names.
You can also set maximum values for user photos in advanced options.

Now you can manage your AD LDS users and e.g. assign groups. You might want to set the default domain name in the profile editor.
Attention:
Password changes require a secure connection via ldaps://. Check your LAM server profile if password changes are refused by the server.


Wildcards
This module provides the following wildcards (others may be provided by other modules). Add a "_" after the "$" to get the value in lower-case (e.g. "$_firstname").
$firstname: First name
$lastname: Last name
$user: User name
$commonname: Common name
$email: Email address
You can use them in the following input fields on user edit screen:
Common name
Display name
Email
Email alias
Use this when some of your data always follows the same schema. E.g. setting "$firstname $lastname" for the common name field can be used like this to get "Demo User". You can set the wildcards in profile editor so they are automatically applied for new users.


You can manage file system quotas with LAM. This requires to setup lamdaemon. LAM connects to your server via SSH and manages the disk filesystem quotas. The quotas are stored directly on the filesystem. This is the default mechanism to store quotas for most systems.
Please add the module "Quota (quota)" for users to your LAM server profile to enable this feature.
If you store the quota information directly inside LDAP please see the next section.

You can store your filesystem quotas directly in LDAP. See Linux DiskQuota for details since it requires quota tools that support LDAP. You will need to install the quota LDAP schema to manage the object class "systemQuotas".
Please add the module "Quota (systemQuotas)" for users to your LAM server profile to enable this feature.
If you store the quota information on the filesystem please see the previous section.

This module supports to manage Kolab accounts with LAM. E.g. you can set the user's mail quota and define invitation policies.
Please add the Kolab user module in your LAM server profile to activate Kolab support.

Please enter an email address at the Personal page and set a Unix password first. Both are required that Kolab accepts the accounts. The email address ("Personal" page) must match your Kolab domain, otherwise the account will not work.

If you upgrade existing non-Kolab accounts please make sure that the account has an Unix password.
LAM supports Asterisk accounts, too. See the Asterisk section for details.
EDU person accounts are mainly used in university networks. You can specify the principal name, nick names and much more.

There are two LAM user modules depending if your user entries should be built on object class "pykotaObject" or a different structural object class (e.g. "inetOrgPerson"). For "pykotaObject" please select "PyKota (pykotaUserStructural(*))" and "PyKota (pykotaUser)" in all other cases.

To display the job history please setup the job DN on tab "Module settings":

Now you can add the PyKota extension to your user accounts. Here you can setup the printing options and add payments for this user.
For LAM Pro there are also self-service fields to allow users e.g. to view their current balance and job history.

You may also view the payment and job history.


OpenLDAP supports the ppolicy overlay to manage password policies for LDAP entries. LAM Pro supports managing the policies and assigning them to user accounts.
Please add the account type "Password policies" to your LAM server profile and activate the "Password policy" module for the user/group/host type.

You can select the password policy and force a password change on next login. Accounts can also be (un)locked.

You can assign any password policy which is found in the LDAP suffix of the "Password policies" type. When you set the policy to "default" then OpenLDAP will use the default policy as defined in your slapd.conf file.
Attention: Locking and unlocking requires that you also activate the option "Lockout users" in the assigned password policy. Otherwise, it will have no effect.
This module allows you to display if users are locked by 389ds server. You can (de)activate your users. The password expiration time can also be managed.
Requirements: 389ds LDAP server
Configuration
Please add the user module "Account locking (locking389ds)".

This will show the password expiration time. You can edit the value if needed.
If there are any failed login attempts then LAM displays their number and till when the user is locked by the system.
The limit of failed login attempts and lockout duration is configured on your LDAP server and not within LAM.

You can unlock the user by clicking on the lock icon.
Here you can also (de)activate the account.
Note: Accounts are only locked by the LDAP server due to failed password attempts. You cannot manually lock an account. Deactivate it in case you want to disable login for a user.

FreeRadius is a software that implements the RADIUS authentication protocol. LAM allows you to manage several of the FreeRadius attributes.
To activate the FreeRadius plugin please activate the FreeRadius user module in your server profile:

You can disable unneeded fields on the tab "Module settings". Here you can also set the DN where your Radius profile templates are stored if you use the option "Profile".

Now you will see the tab "FreeRadius" when editing users. The extension can be (de)activated for each user. You can setup e.g. realm, IP and expiration date.

You can manage your Heimdal Kerberos accounts with LAM Pro. Please add the user module "Kerberos (heimdalKerberos)" to activate this feature.
Setup password changing
LAM Pro cannot generate the password hashes itself because Heimdal uses a proprietary format for them. Therefore, LAM Pro needs to call e.g. kadmin to set the password.
The wildcards @@password@@ and @@principal@@ are replaced with password and principal name. Please use keytab authentication for this command since it must run without any interaction.
Example to create a keytab: ktutil -k /root/lam.keytab add -p lam@LAM.LOCAL -e aes256-cts-hmac-sha1-96 -V 1
Security hint: Please secure your LAM Pro server since the new passwords will be visible for a short term in the process list during password change.

User management
You can specify the principal/user name, ticket lifetimes and expiration dates. Additionally, you can set various account options.

You can manage your MIT Kerberos accounts with LAM Pro. Please add the user module "Kerberos (mitKerberos)" to activate this feature. If you want to manage entries based on the structural object class "krbPrincipal" please use "Kerberos (mitKerberosStructural)" instead.
Setup password changing
LAM Pro cannot generate the password hashes itself because MIT uses a proprietary format for them. Therefore, LAM Pro needs to call kadmin/kadmin.local to set the password.
LAM will add "-q 'cpw -pw PASSWORD PRINCIPAL'" to the command to set the password. Please use keytab authentication for this command since it must run without any interaction.
Keytabs may be created with the "ktutil" application.
Security hint: Please secure your LAM Pro server since the new passwords will be visible for a short term in the process list during password change.
Please note that kadmin/kadmin.local often returns a successful command even if errors occurred (e.g. password policy violations). You need to test this before and if affected then write a wrapper script around kadmin that returns non-zero return codes for errors.
Example commands:
/usr/sbin/kadmin -k -t /home/www-data/apache.keytab -p realm/changepwd
sudo /usr/sbin/kadmin.local

User management
You can specify the principal/user name, ticket lifetimes and expiration dates. Additionally, you can set various account options.

This module allows to add/remove the user in mail alias entries.
Note: You need to activate the mail alias type for this module.
To activate mail aliases for users please select the module "Mail aliases (nisMailAliasUser)":

On tab Module settings you can select if you want to set the user name or email as recipient in alias entries.

Now you will see the mail aliases tab when editing an user.
The red cross will only remove the user from the alias entry. If you click the trash can button then the whole alias entry (which may contain other users) will be deleted.

You can add the user to existing alias entries or create completely new ones.

This module allows to add/remove the Courier extension for users.
Configuration:
Please activate the module Courier for users to enable this extension. The Unix module is optional.

Usage:
Your user tab will now show the Courier extension. This can be added/removed any time.
Here you can configure the home directory in case the Unix module is not activated. Additionally, mailbox folder, quota, server and feature flags can be configured.

LAM Pro manages all qmail attributes for users. This includes mail addresses, ID numbers and quota settings.
Please note that the main mail address is managed on tab "Personal" if this module is active. Otherwise, it will be on the qmail tab.

You can hide several qmail options if you do not want to manage them with LAM. This can be done on the module settings tab of your LAM server profile.

LAM supports to manage mail routing for user accounts.
Module activation:
This feature can be activated by adding the "Mail routing" module to the user account type in your server profile.

Usage
You can specify a routing address, the mail server and a number of local addresses to route.
In case you want to add this extension by default for new users there is an option in profile editor.

Wildcards
The module supports wildcards in the following input fields:
Routing address
Local address
See the other modules that you activated what wildcards they provide (e.g. $user).
You can manage your public keys for SSH in LAM if you installed the LPK patch for SSH or setup AuthorizedKeysCommand (see below).
Activate the "SSH public key" module for users in the server profile and you can add keys to your user entries.


Example for AuthorizedKeysCommand
This will dynamically get the public key from LDAP. In this case there is no need to patch SSH sources.
Create the authentication script in e.g. /usr/bin/ldapAuthSSH.sh
#!/bin/bash
uid=$1
server=ldap.domain.com
baseDN=ou=people,dc=example,dc=com
port=389
ldapsearch -x -h $server -p $port -b $baseDN -s sub "(&(objectclass=posixAccount)(uid=$uid))" | sed -n '/^ /{H;d};/sshPublicKey:/x;$g;s/\n *//g;s/sshPublicKey: //gp'
Now setup your sshd_config
AuthorizedKeysCommand /usr/bin/ldapAuthSSH.sh
AuthorizedKeysCommandUser root
You can manage your public SSH keys in Active Directory/Samba 4. Activate the "SSH public key (AD)" module for users in the server profile and you can add keys to your user entries. This will use the attribute "altSecurityIdentities".
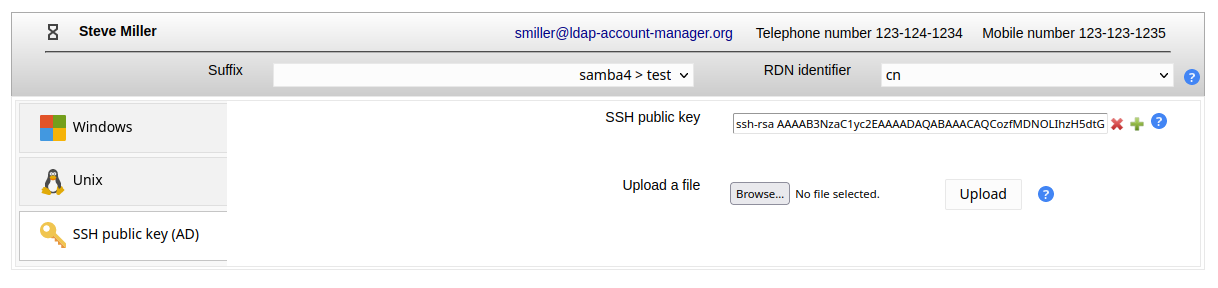
Example for AuthorizedKeysCommand
This will dynamically get the public key from LDAP.
Create the authentication script in e.g. /usr/bin/ldapAuthSSH.sh
#!/bin/bash
uid=$1
server=ldap.domain.com
baseDN=ou=people,dc=example,dc=com
port=389
ldapsearch -x -h $server -p $port -b $baseDN -s sub "(&(objectclass=posixAccount)(uid=$uid))" | sed -n '/^ /{H;d};/altSecurityIdentities:/x;$g;s/\n *//g;s/altSecurityIdentities: //gp'
Now setup your sshd_config
AuthorizedKeysCommand /usr/bin/ldapAuthSSH.sh
AuthorizedKeysCommandUser root
You can manage your YubiKey ids with LAM. It supports the yubiKeyUser schema or any other attribute mapping.
Configuration
First, you need to activate the YubiKey module for users in your LAM server profile.

Second, you need to specify which object class and attribute name should be used.
Object class: If you have an object class just for the YubiKey ids then enter it here. LAM will then provide options to add and remove it. In case you reuse some existing attribute from e.g. inetOrgPerson please leave object class name blank.
Attribute name: please enter the attribute name that is used for the key ids.

You will then be able to manage the key ids for your users.

Self-service (LAM Pro)
This will allow your users to update their own keys.
You need to configure the object class and attribute name first. This is done on tab "Module settings" in self-service profile.
Attention: Please note that both fields are mandatory here. Even if you reused an attribute from some existing object class you need to set it here. LAM needs this to detect if the user can add keys.

Then add the YubiKey ids field to your self-service profile on tab "Page layout".

When a user with the specified object class logs in then the key input fields are shown.

You can setup PAM to check if a user is allowed to run a specific service (e.g. sshd) by reading the LDAP attribute "authorizedService". This way you can manage all allowed services via LAM.
To activate this PAM feature please setup your /etc/libnss-ldap.conf and set "pam_check_service_attr" to "yes".
Inside LAM you can now set the allowed services. You may also setup default services in your account profiles.

You can define a list of services in your LAM server profile that is used for autocompletion.

The autocompletion will show all values that contains the entered text. To display the whole list you can press backspace in the empty input field. Of course, you can also insert a service name that is not in the list.

LAM may create and delete mailboxes on an IMAP server for your user accounts. You will need an IMAP server that supports either SSL or TLS for this feature.
To activate the mailbox management module please add the "Mailbox (imapAccess)" module for the type user in your LAM server profile:

Now configure the module on the tab "Module settings". Here you can specify the IMAP server name, encryption options, the authentication for the IMAP connection and the valid mail domains. LAM can use either your LAM login password for the IMAP connection or display a dialog where you need to enter the password. It is also possible to store the admin password in your server profile. This is not recommended for security reasons.
The user name can either be a fixed name (e.g. "admin") or it can be generated with LDAP attributes of the LAM admin user. E.g. $uid$ will be transformed to "myUser" if you login with "uid=myUser,ou=people,dc=example,dc=com".
The mail domains specify for which accounts mailboxes may be created/deleted. E.g. if you enter "lam-demo.org" then mailboxes can be managed for "user@lam-demo.org" but not for "user@example.com". Use "*" for any domain.
You need to install the SSL certificate of the CA that signed your server certificate. This is usually done by installing the certificate in /etc/ssl/certs. Different Linux distributions may offer different ways to do this. For Debian/Ubuntu please copy the certificate in "/usr/local/share/ca-certificates" and run "update-ca-certificates" as root.
It is not recommended to disable the validation of IMAP server certificates.
The prefix, user name attribute and path separator specifies how your mailboxes are named (e.g. "user.myUser@localhost" or "user/myUser"). Select the values depending on your IMAP server settings.
You can specify a list of initial folder names to create for new mailboxes. LAM will then create them with each new mailbox.

When you edit an user account then you will now see the tab "Mailbox". Here you can create/delete the mailbox for this user.
Please note that mailbox creation via file upload is not possible if you configured in LAM server profile to ask for the admin password.

You can manage the IP addresses of user accounts (e.g. assigned by DHCP) with the ipHost module.
Configuration

User editing

This is a very simple module to manage accounts based on the object class "account". Usually, this is used for host accounts only. Please pay attention that users based on the "account" object class cannot have contact information (e.g. telephone number) as with "inetOrgPerson".
You can enter a user/host name and a description for your accounts.

Use this module if you want to use OpenLDAP's builtin 2-factor-authentication with TOTP.
For admin interface add the OpenLDAP TOTP module:

When one of your users activates TOTP then you can see the serial number and TOTP params in user edit screen.
Please note that the token can only be setup by the user in self service. Admins are not able to setup tokens. They can just delete them by removing the extension.

This module shows the last successful login of the user. You can setup a cron job to deactivate inactive users.


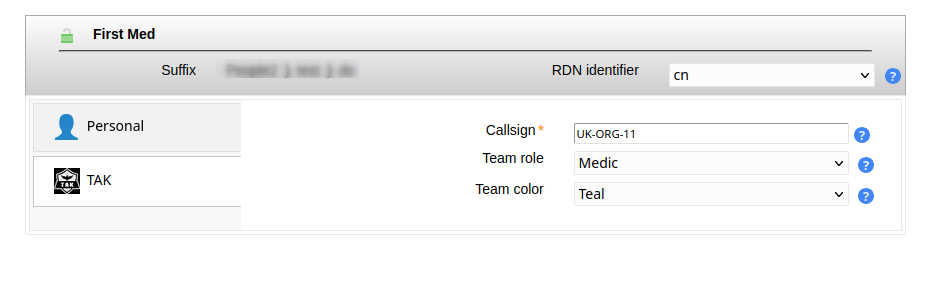
The TAK module supports the Team Awareness Kit or Tactical Assault Kit (TAK) with the Android Team Awareness Kit (ATAK).
You can define callsigns, team roles and colors for users.
LDAP schema
The module expects that TAK users use the object class "takUser" and the attributes "takCallsign", "takRole" and "takColor". You can find matching schema files in /usr/share/ldap-account-manager/docs/schema (DEB/RPM) or docs/schema (tar.bz2). Please see the beginning of the files for installation instructions.
OpenLDAP: tak-OpenLDAP.ldif
Samba 4: tak-Samba4-attributes.ldif and tak-Samba4-objectClass.ldif
Windows (AD): tak-Windows.ldif
Configuration
Add the TAK module for users in your server profile:
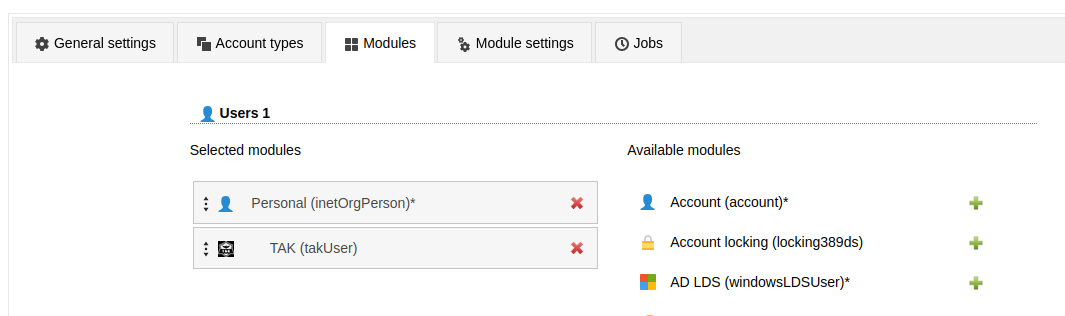
Now you can manage the TAK attributes for users.
LAM Pro users can add these attributes to the self-service profile if needed.